Monitor Emerging Threat Activity Across Trusted Sources
Track new public reporting from the sources your team trusts, extract the intelligence that matters, and act on it faster.
Overview
Threat activity rarely arrives in a clean, centralised feed. It appears across vendor blogs, incident writeups, research notes, and campaign updates published at different times, in different formats, and with different levels of detail. Analysts are left checking too many sources, rereading the same material in multiple places, and manually pulling out the parts that are actually useful.
Obstracts helps teams monitor emerging threat activity across the sources they trust without turning that monitoring process into more manual work. It continuously collects reporting from subscribed feeds, preserves the historical record of what has been published, and converts each post into structured threat intelligence that can be searched, reviewed, exported, and operationalised.
The result is simple: instead of monitoring blogs as disconnected documents, you monitor them as a live intelligence source.
What this solves
Most teams already know which public sources they care about. The problem is not identifying useful sources. The problem is keeping up with them consistently, then turning what they publish into something analysts can use.
That challenge usually breaks down into four separate issues:
- Important updates are spread across too many places to track reliably by hand.
- New posts need to be reviewed quickly, but most of the content is still unstructured narrative.
- Indicators, ATT&CK techniques, malware names, actors, and relationships have to be extracted before they can be used downstream.
- Analysts need a fast way to pivot from a new report to related reporting, prior sightings, and connected activity.
When those steps are handled manually, monitoring breaks down. Sources get checked inconsistently. Context is lost between reports. Intelligence stays trapped inside browser tabs, screenshots, and analyst notes.
Obstracts addresses that by making source monitoring continuous and making each new post immediately usable as structured intelligence.
How Obstracts helps you monitor threat activity
Obstracts ingests the sources you choose and keeps them updated over time. As new posts appear, they are pulled into a single place for review. Historical content is also preserved, which means monitoring is not limited to whatever happened to be published today. Teams can work from the full record of a source, not just its latest update.
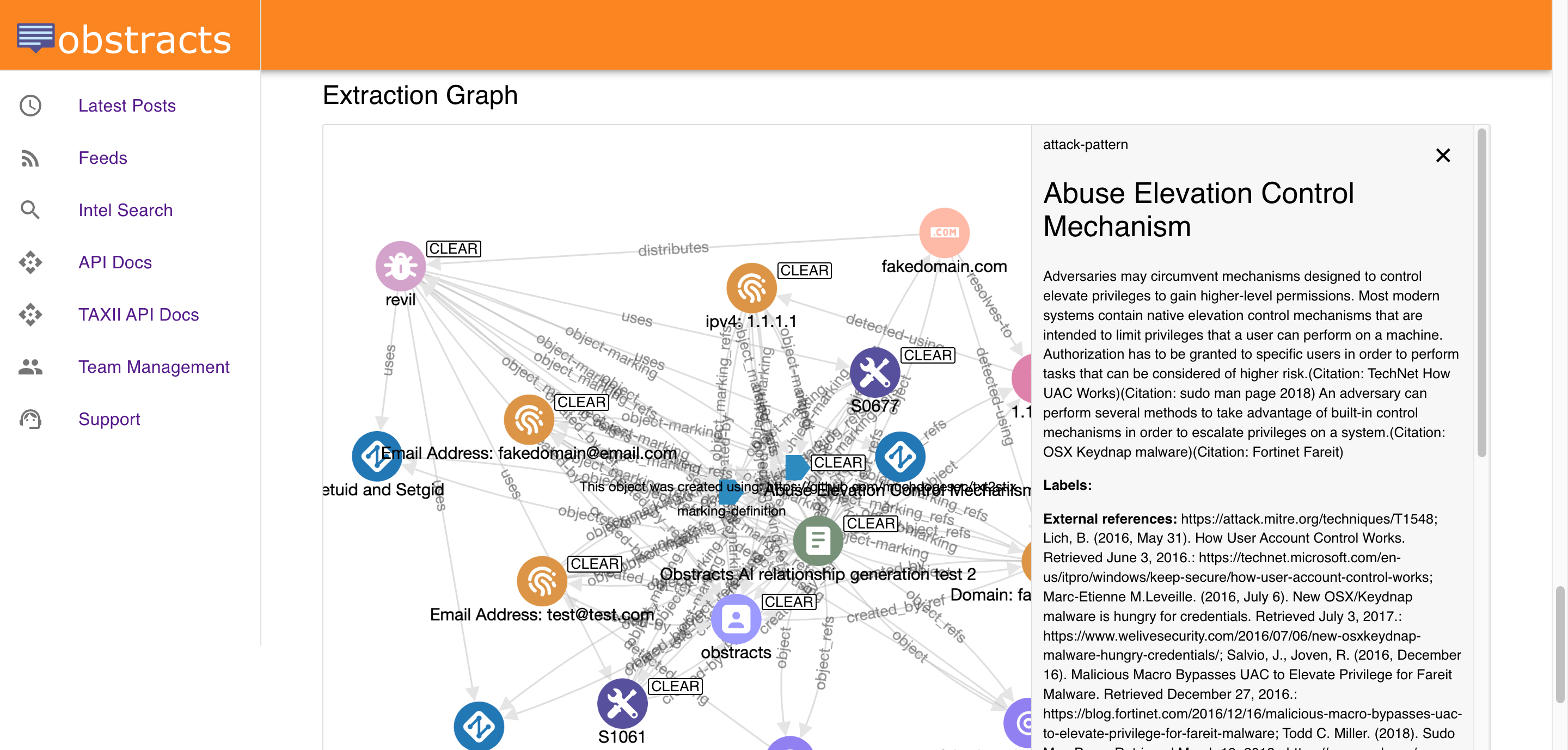
Each post is then processed so analysts do not have to start from raw text every time. Obstracts extracts indicators of compromise, ATT&CK-aligned TTPs, and other relevant entities and relationships from the reporting, storing them as STIX 2.1 objects. This gives your team two things at once: the original source material for context, and the structured intelligence needed for search, enrichment, and downstream use.
That changes the monitoring workflow in a meaningful way. Instead of asking, “Has anyone published something new?” teams can ask better questions:
- Which new reports mention the infrastructure, malware family, or actor we care about?
- What techniques are appearing more often across recent reporting?
- Which themes or grouped topics are starting to emerge across trusted sources?
- Which sources are discussing the same activity from different angles?
- What new intelligence should be reviewed, enriched, or pushed into other systems?
From source monitoring to usable intelligence
Fast monitoring matters, but speed without structure still leaves work for the analyst. A new post may contain valuable information, but if that information remains buried in prose, it cannot be searched effectively, compared easily, or moved downstream without another round of manual effort.
Obstracts closes that gap. It does not stop at collecting source material. It turns public reporting into a dataset your team can work with.
That means analysts can move from source to signal much faster:
- Review newly published reporting in one place instead of jumping between sites.
- See extracted observables and behaviours without manually copying them out of the article.
- Search across reporting by IoC, ATT&CK technique, malware, threat actor, or other structured object.
- Pivot from one object to every report in which it appears.
- Export or integrate the resulting intelligence into the rest of the security stack.
This is especially useful when a fast-moving campaign is being covered by multiple trusted publishers over a short period of time. Instead of reviewing each post in isolation, analysts can quickly identify overlaps, repeated infrastructure, recurring techniques, and newly introduced artefacts.
Why trusted sources still need automation
Security teams do not want more sources. They want better coverage of the sources they already trust. That is exactly why automation matters here.
Even a relatively focused source list creates significant monitoring overhead. A team following vendor research blogs, select incident response firms, malware researchers, and internal priority sources can easily end up tracking dozens or hundreds of feeds. The problem compounds when those feeds publish unevenly. Some may stay quiet for days, then release several important posts in quick succession. Others may post frequently, but only occasionally include material relevant to your environment or investigations.
Manual monitoring does not scale cleanly in that environment. It introduces delays, inconsistency, and avoidable blind spots. Obstracts gives teams a way to stay close to trusted public reporting without dedicating analyst time to repetitive collection and extraction work.
This makes monitoring more sustainable. Analysts can spend their time assessing significance, validating relevance, and taking action instead of repeatedly checking whether a site has published something new.
What analysts can do once new activity appears
Monitoring only matters if it leads to useful next steps. Once new reporting is ingested and structured, Obstracts supports the kinds of actions analysts actually need to take.
An analyst might begin with a fresh report describing phishing infrastructure, credential harvesting domains, and specific ATT&CK techniques. From there they can search for those same domains across prior reporting, identify whether the techniques have appeared in recent campaigns, review other posts referencing the same malware family, and export the structured results for use elsewhere.
Another team might use Obstracts to keep track of emerging activity tied to a region, sector, or intrusion set they care about. Rather than monitoring individual posts in isolation, they can build a more connected view of how public reporting is evolving over time.
Because the intelligence is structured, the output is not limited to reading and search. Teams can use it for enrichment, internal triage, CTI production workflows, and integration with platforms that support STIX or TAXII-based consumption.
Where this fits in a modern CTI or SOC workflow
Obstracts is useful anywhere public threat reporting is part of the workflow.
For threat intelligence teams, it reduces the gap between publication and usable intelligence. For SOC teams, it provides a practical way to monitor relevant public reporting and surface the indicators and behaviours worth actioning. For research-heavy teams, it creates a searchable, connected intelligence layer across many sources instead of forcing repeated manual review of source websites.
It is also a strong fit for organisations that already have downstream systems in place but want a better upstream collection and structuring layer. If your team already uses STIX, TAXII, OpenCTI, or internal enrichment pipelines, Obstracts can help turn trusted public reporting into something those systems can consume more easily.
Why this approach is effective
The value of monitoring emerging threat activity is not just knowing that a new blog post exists. The value is recognising what is in that post, how it connects to existing knowledge, and how quickly your team can act on it.
Obstracts is effective because it supports that full path:
- Continuous monitoring of subscribed sources
- Historical visibility across prior reporting
- Automatic extraction of structured intelligence
- Search and pivoting across connected objects and reports
- Export and integration through standard CTI workflows
That combination helps teams move from passive source monitoring to active intelligence use. Public reporting becomes easier to track, easier to search, and easier to operationalise.
Monitor faster, respond sooner
If your team depends on public reporting to stay current on adversary behaviour, malware activity, infrastructure, or emerging campaigns, the limiting factor is usually not access to information. It is the time required to collect it, review it, extract it, and connect it.
Obstracts removes much of that friction. It helps you monitor trusted sources continuously, turns new reporting into structured intelligence, and makes it easier for analysts to find what matters and act on it quickly.
That is what effective monitoring should look like: less time checking sources, less time extracting data by hand, and more time using intelligence.
Explore next
- Want the higher-level outcome view? See Operationalise Public Threat Intelligence.
- Want to pivot from new reporting into specific objects and context? See Enrich IoCs and TTPs with Public Threat Intelligence.
- Want to turn ongoing monitoring into faster analyst workflows? See Accelerate Threat Research and Investigation.
