Map Public Reporting to MITRE ATT&CK and Attack Flows
Turn unstructured reporting into ATT&CK-aligned techniques, ordered attack flows, and connected intelligence you can use for defence, detection, and emulation.
Overview
Public threat reporting often contains the detail defenders need, but not in a format they can act on quickly. Useful information is buried in narrative text: techniques are described in prose, attack stages are spread across paragraphs, and the relationship between one report and another is hard to see without manual reading and comparison.
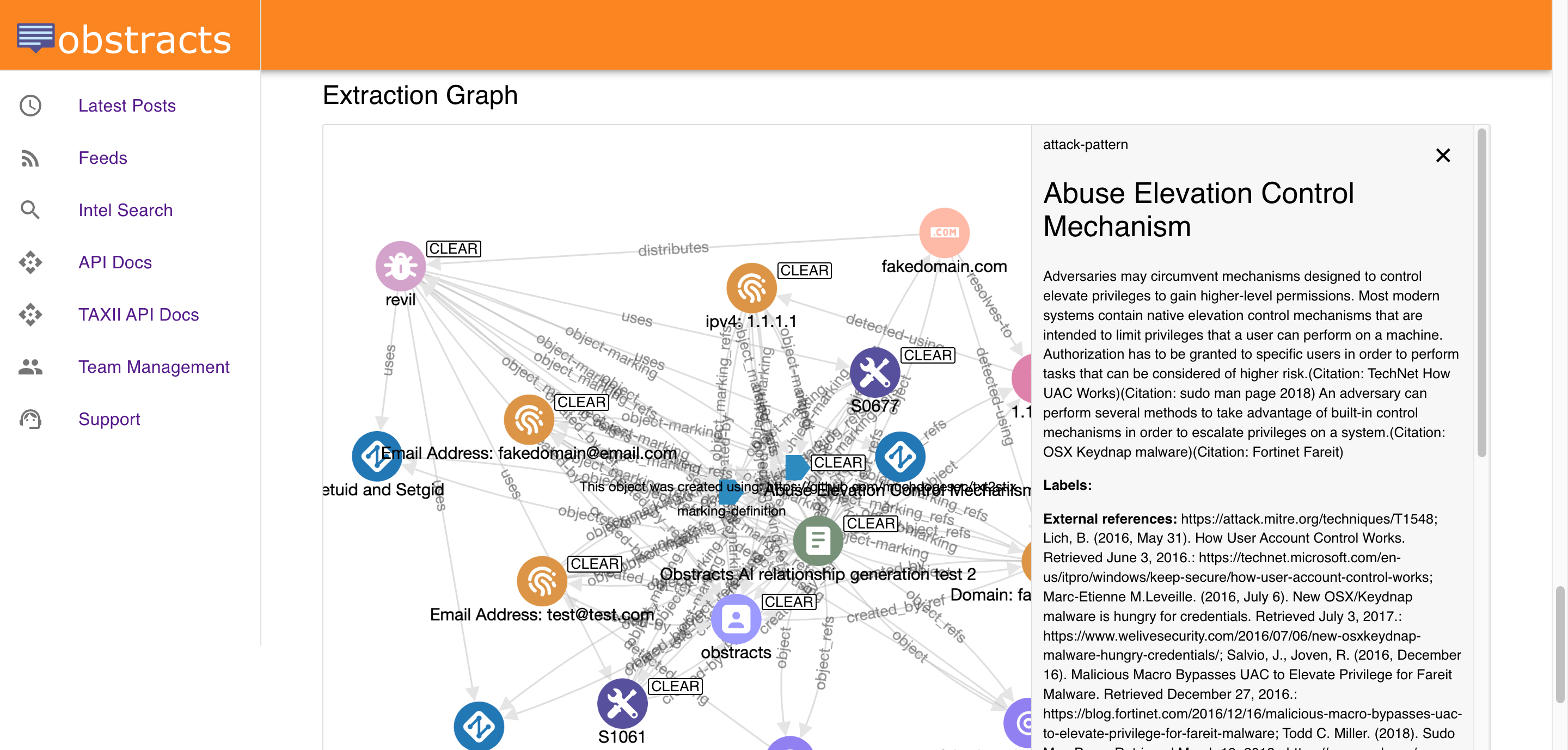
Obstracts helps teams turn that reporting into something operational. It extracts ATT&CK-aligned techniques, preserves the ordering of adversary behaviour through Attack Flows, and makes it easier to correlate related reporting across multiple sources. Instead of reading each post as a standalone document, analysts can use public reporting as structured intelligence for defensive coverage, investigation, and testing.
This matters because ATT&CK mapping on its own is useful, but incomplete. A list of techniques tells you what appeared in a report. An ordered flow helps you understand how those behaviours fit together.
What this solves
Most defenders do not struggle to find ATT&CK references. They struggle to use them consistently across large volumes of public reporting.
The usual problems are familiar:
- Techniques are mentioned in different ways across different reports and need to be normalised.
- Reports describe adversary behaviour, but not in a way that is easy to sequence or compare.
- Analysts can identify individual TTPs, but still lack a clear view of how an intrusion unfolded.
- Similar activity appears across multiple posts, but those connections are easy to miss when each report is reviewed in isolation.
- Detection, hunting, and emulation teams need structured outputs, not another set of browser tabs and notes.
Obstracts addresses those issues by turning narrative reporting into ATT&CK-tagged, flow-aware, connected intelligence.
ATT&CK tagging that supports real analysis
ATT&CK tagging is valuable because it gives defenders a shared language for adversary behaviour. When techniques are mapped consistently, teams can search activity more easily, compare reporting faster, and align intelligence with detections, controls, and coverage reviews.
Obstracts extracts TTPs from public reporting and maps them into ATT&CK-aligned structured data. That gives analysts a practical way to move beyond keyword search and into technique-driven analysis.
With ATT&CK tagging in place, teams can:
- Search reporting by specific ATT&CK techniques.
- Identify which behaviours are showing up repeatedly across recent publications.
- Review activity by technique rather than by source alone.
- Connect public reporting to internal coverage assessments and detection engineering priorities.
- Build a cleaner bridge between CTI, SOC, purple team, and threat hunting workflows.
This is important because ATT&CK is often most useful when it becomes a pivot point. A defender may start with one technique seen in an incident, control gap, or hypothesis, then use that technique to find related reporting, adjacent behaviours, and other campaigns that show similar tradecraft.
Obstracts makes that style of workflow easier by structuring the techniques found in each report rather than leaving them embedded in prose.
Why attack ordering matters
A flat list of TTPs is only part of the story. Defenders also need to understand order, progression, and dependency.
An intrusion is not just a collection of behaviours. It is a sequence. Initial access is followed by execution, persistence, credential access, discovery, lateral movement, collection, exfiltration, or impact. Even when a report does not describe every stage, the ordering of the behaviours it does describe can still be highly useful.
That is where Attack Flows matter. Obstracts goes beyond simple technique extraction by building ordered representations of the adversary behaviour described in reporting. This helps analysts understand not only which techniques were used, but how they were used together.
That added structure supports better defensive thinking:
- Coverage planning becomes easier because teams can assess not just whether they detect a technique, but whether they can observe the broader sequence around it.
- Hunting improves because analysts can move from a known technique to the steps likely to appear before or after it.
- Investigation becomes faster because defenders can review the attack path described in public reporting rather than reconstructing it manually.
- Emulation becomes more realistic because purple teams and red teams can test ordered behaviour chains instead of isolated ATT&CK techniques.
This is one of the most useful distinctions between simple ATT&CK tagging and more complete adversary modelling. A technique list is helpful for classification. An attack flow is more useful for operational planning.
Better support for defence coverage
One practical use of ATT&CK-aligned public reporting is identifying gaps in defensive coverage.
Teams often review ATT&CK coverage in theory, but the most useful validation comes from observed behaviour. Public reporting provides examples of how real adversaries combine techniques in real intrusions. When that reporting is structured, it becomes much easier to compare it against existing detections, telemetry, controls, and playbooks.
Obstracts helps make that comparison faster. Teams can review which techniques are appearing in current reporting, examine how they are ordered in an attack flow, and ask more useful defensive questions:
- Do we have meaningful visibility for these behaviours?
- Can we detect only the headline technique, or also the surrounding steps?
- Are we prepared for the full intrusion path described in recent reporting?
- Which ATT&CK techniques are showing up often enough to justify new detection work?
This turns public reporting into a more practical input for coverage reviews. Instead of discussing ATT&CK at a framework level alone, teams can anchor those discussions in recent observed activity.
Better support for threat hunting and intrusion analysis
Attack-flow context is also useful when analysts are looking for signs of intrusion inside their own environment.
If a team sees evidence of one technique, they rarely want to stop there. They want to know what is likely connected to it. What came before it? What tends to come next? What other behaviours appear alongside it in real campaigns?
Obstracts helps answer those questions by preserving ordered behaviour from reporting and making it searchable. Analysts can begin from a technique, malware family, actor, or other object and work outward into related intelligence.
That supports more focused hunting:
- Start with a suspicious technique already observed internally.
- Review public reporting that contains the same or similar behaviour.
- Look at the ordered attack flow to identify adjacent stages worth searching for.
- Pivot into related reports that share techniques, infrastructure, malware, or other connected objects.
This is especially useful when defenders are working from incomplete evidence. Public reporting will never mirror an internal incident perfectly, but structured ATT&CK and Attack Flow data can still provide a strong model for what to investigate next.
Correlate related posts and pivot on similarities
Another major challenge with public reporting is fragmentation. Multiple vendors may cover the same campaign, overlapping infrastructure, the same malware family, or the same cluster of TTPs, but they may do so using different wording, different depth, and different framing.
When those reports are read one by one, it is easy to miss similarities. Obstracts helps reduce that problem by structuring the entities and behaviours found in each post so analysts can correlate and pivot more effectively.
This matters in several ways:
- A technique seen in one report can be used to find other reports describing similar tradecraft.
- Shared infrastructure or malware references can reveal overlap between campaigns or reporting streams.
- Repeated behaviour patterns can help analysts identify common attacker workflows even when attribution differs.
- Multiple posts can be reviewed together to build a more complete picture than any single source provides.
In practice, this means a defender can move from “this report is interesting” to “show me everything related to this behaviour pattern.” That is a much more useful workflow for CTI, hunting, and defensive planning.
More useful output for emulation and purple teaming
Public reporting is often used as inspiration for ATT&CK emulation, but turning it into a realistic test plan takes work. Teams need to extract the relevant techniques, decide what matters, order the activity, and convert that into something actionable.
Obstracts reduces that preparation burden.
By extracting ATT&CK-aligned techniques and preserving attack ordering, it gives emulation teams a better starting point for reproducing adversary behaviour. Rather than selecting disconnected techniques from a report, they can work from a more faithful behavioural chain.
That is useful for:
- ATT&CK emulation planning
- Purple team scenario design
- Detection validation against realistic attack paths
- Prioritising test cases based on recently observed public reporting
This does not replace analyst judgement. Teams still need to decide what is relevant to their environment and what can be tested safely. But it does make the source material much easier to work with.
Where this fits in the workflow
Obstracts fits best where teams want to operationalise ATT&CK-oriented public intelligence instead of just reading it.
For CTI teams, it creates a structured layer over public reporting that is easier to analyse and share. For SOC teams, it turns external reporting into something that can support triage, hunting, and detection improvement. For purple teams, it provides a cleaner path from public writeup to emulation scenario. For security leaders, it provides a more concrete way to relate external adversary behaviour to internal coverage questions.
It is also a strong fit for organisations already using STIX, TAXII, ATT&CK Navigator, OpenCTI, or internal workflows that benefit from structured behavioural data. Obstracts helps public reporting enter those systems in a form that is more consistent and more useful.
What makes this approach effective
The value here does not come from ATT&CK labels alone. It comes from combining several pieces that are often separated in practice:
- ATT&CK tagging for normalised technique-level analysis
- Attack Flow ordering for behavioural context
- Correlation across reports for similarity analysis and pivoting
- Structured outputs that can support downstream defensive workflows
That combination gives teams a better way to work with public adversary reporting. It is easier to search, easier to compare, easier to turn into defence coverage decisions, and easier to use for investigation or emulation.
From ATT&CK references to operational context
If your team uses MITRE ATT&CK as part of detection engineering, threat hunting, CTI analysis, or purple teaming, public reporting can be one of the most useful sources of current adversary behaviour. The challenge is making that reporting usable at speed and at scale.
Obstracts helps close that gap. It turns public reporting into ATT&CK-aligned structured intelligence, adds behavioural ordering through Attack Flows, and makes it easier to correlate related posts across trusted sources.
That gives defenders something more useful than a list of articles to read. It gives them a practical way to search behaviour, understand attack progression, compare related reporting, and apply those insights to defence.
Explore next
- Want the broader outcome this enables? See Improve Detection and Hunting with Structured Threat Intelligence.
- Want to start from a specific technique or observable and enrich it further? See Enrich IoCs and TTPs with Public Threat Intelligence.
- Want to feed ATT&CK and attack-flow data into other tools? See Integrate Obstracts into Your Security Stack and AI Workflows.
