Improve Detection and Hunting with Structured Threat Intelligence
Use ATT&CK-aligned techniques, attack flows, and connected public intelligence to strengthen detection engineering, hunting, and defensive coverage.
Overview
Detection and hunting workflows improve when defenders can work from real observed behaviour instead of isolated indicators or abstract framework references.
Public reporting contains that behaviour, but it is often hard to use directly. Techniques are embedded in narrative text, attack progression has to be reconstructed manually, and related reporting is difficult to compare at speed.
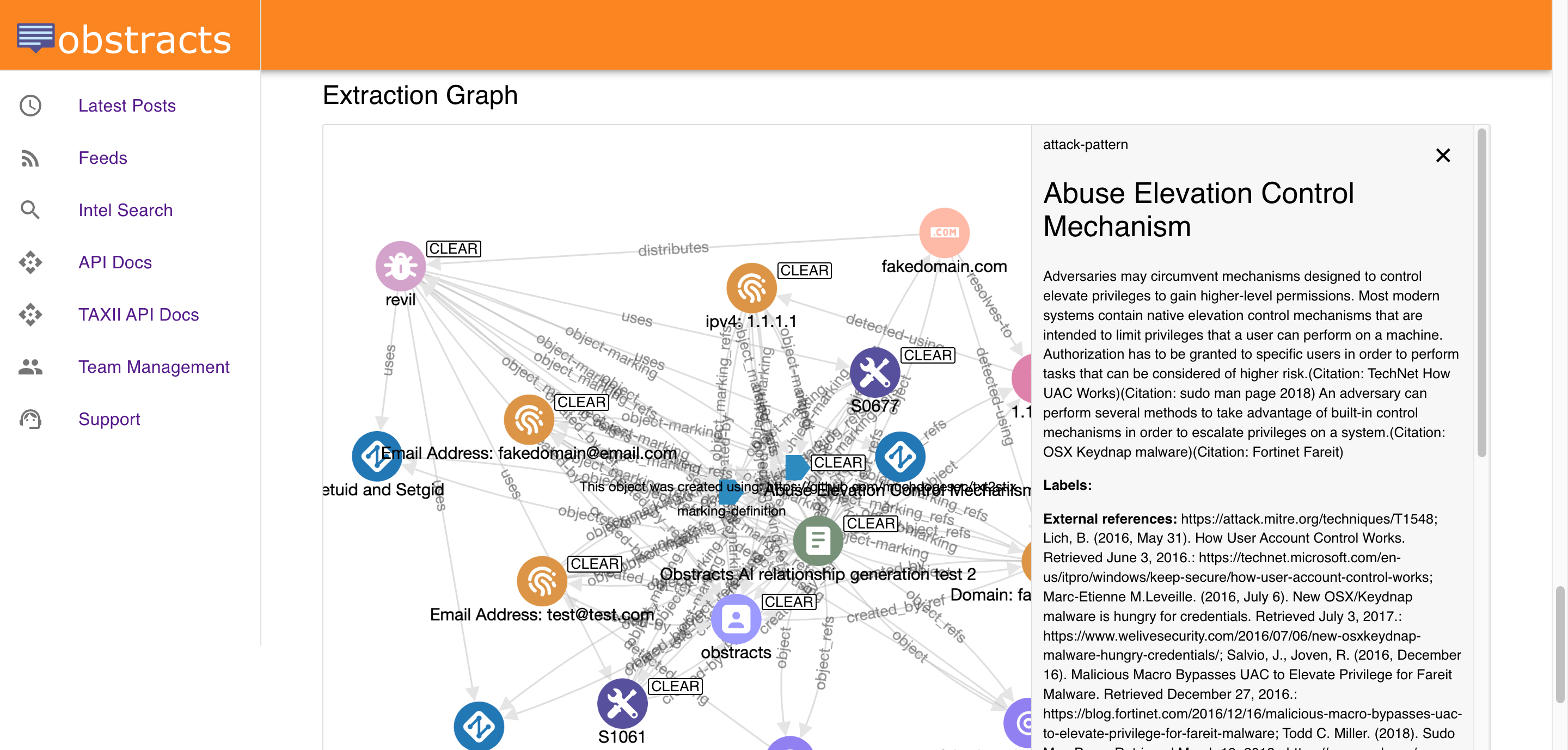
Obstracts helps turn that into a stronger defensive workflow. It maps reporting to MITRE ATT&CK, preserves adversary behaviour through Attack Flows, and makes it easier to correlate related activity across sources.
What this outcome looks like
Improving detection and hunting with structured threat intelligence means defenders can:
- Search for current tradecraft by ATT&CK technique
- Understand how techniques fit together in a broader intrusion path
- Use public reporting to guide hunts and detection improvements
- Compare external behaviour with internal telemetry and coverage
- Move from one observed behaviour to related reports, patterns, and context
This is more useful than simply collecting more indicators. It helps teams think in terms of attacker behaviour and defensive visibility.
Why this matters
Defenders often know the framework they want to use. The challenge is grounding it in current, usable intelligence.
Without structure:
- ATT&CK references stay high level
- Hunting starts from incomplete context
- Coverage reviews are harder to tie to recent observed activity
- Emulation planning takes more manual preparation
Structured public intelligence makes those workflows more practical.
Where Obstracts fits
Obstracts helps teams use public reporting as a behavioural intelligence source.
Instead of only reading about techniques, defenders can search them, connect them, sequence them, and compare them across reporting. That supports:
- Detection engineering
- Threat hunting
- Coverage reviews
- Purple teaming and emulation planning
- Investigation workflows that need attack progression and context
What makes this a solution, not just a feature
The outcome comes from combining several capabilities:
- ATT&CK tagging for shared behavioural language
- Attack Flow ordering for progression and context
- Correlation across reporting for similarity analysis
- Structured outputs that can support downstream defensive systems
Together, these help teams move from “we saw this technique mentioned” to “we understand how this behaviour works and what to do next.”
