Operationalise Public Threat Intelligence
Turn public reporting into structured intelligence that can be monitored, searched, enriched, shared, and acted on across your security workflows.
Overview
Public threat reporting is valuable, but it often arrives in the least operational format possible. It is spread across many sources, published at different times, written in different styles, and packed with useful detail that still needs to be extracted before it can support action.
That creates a common gap for security teams. They have access to public intelligence, but not always in a form they can use quickly. Analysts end up monitoring sources manually, copying out indicators, comparing related writeups by hand, and moving context into other systems one step at a time.
Obstracts helps close that gap. It turns public reporting into structured threat intelligence that can be monitored continuously, searched directly, enriched through pivots and correlation, and shared into the rest of the security stack.
What this outcome looks like
Operationalising public threat intelligence means making it part of the working environment, not leaving it as background reading.
In practice, that means:
- Monitoring trusted public sources without repeated manual checking
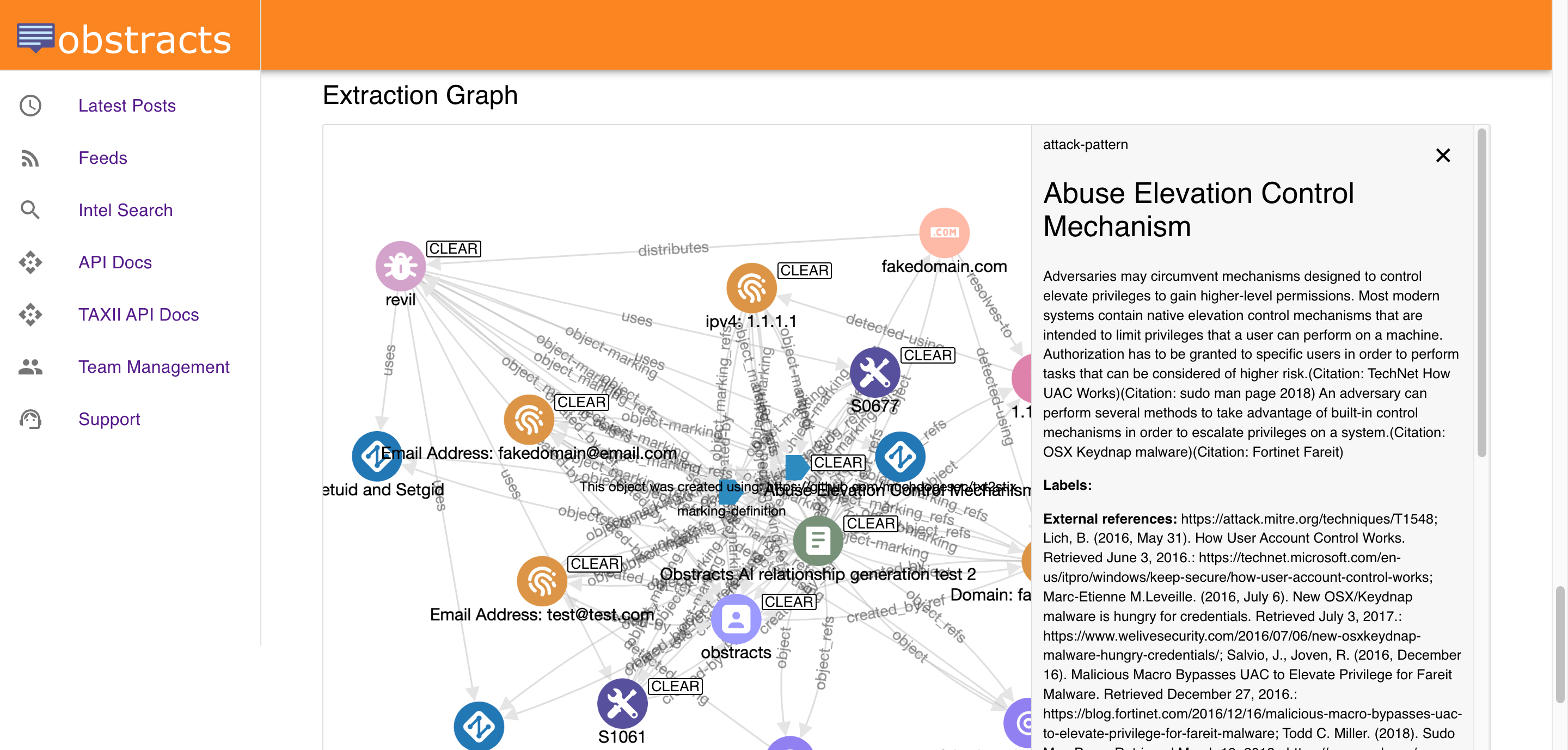
- Extracting IoCs, TTPs, and relationships into structured intelligence
- Searching and pivoting across connected reporting instead of isolated posts
- Moving intelligence into downstream platforms and workflows
- Giving CTI, SOC, hunting, and detection teams a more usable source of external context
The benefit is not just efficiency. It is consistency. Teams can work from the same intelligence layer instead of rebuilding context from scratch each time they need it.
Why this matters
Public reporting is often one of the fastest sources of emerging adversary behaviour, infrastructure, and campaign detail. But its value drops quickly if it takes too long to collect, interpret, and operationalise.
When that process is manual:
- Important updates are easier to miss
- Useful context stays trapped in browser tabs and analyst notes
- External intelligence is harder to compare with internal findings
- Downstream teams receive less usable output
Operationalising public intelligence solves that by making reporting more searchable, more structured, and easier to distribute.
Where Obstracts fits
Obstracts helps teams move from passive consumption to active use.
It supports the full path from source monitoring to structured extraction to downstream use. That means teams can start with new reporting, identify what matters, pivot into related intelligence, and push the result into the workflows that need it next.
This supports a wide range of teams:
- CTI teams that need faster access to usable public intelligence
- SOC teams that need context during triage and investigation
- Threat hunters who need structured behaviour and related reporting
- Detection engineers who need current external tradecraft to work from
- Security engineering teams building integrations, automations, or internal tooling
What makes this a solution, not just a feature
The value is not any one capability in isolation. It is the way the pieces fit together:
- Continuous monitoring gives teams better visibility into new reporting
- Structured extraction makes that reporting easier to search and use
- Correlation and pivoting turn isolated posts into connected intelligence
- Export and integration make the intelligence available outside the platform
That combination is what turns public reporting into a working intelligence source.
